| #!/usr/bin/env bash | |
| # checks if branch has something pending | |
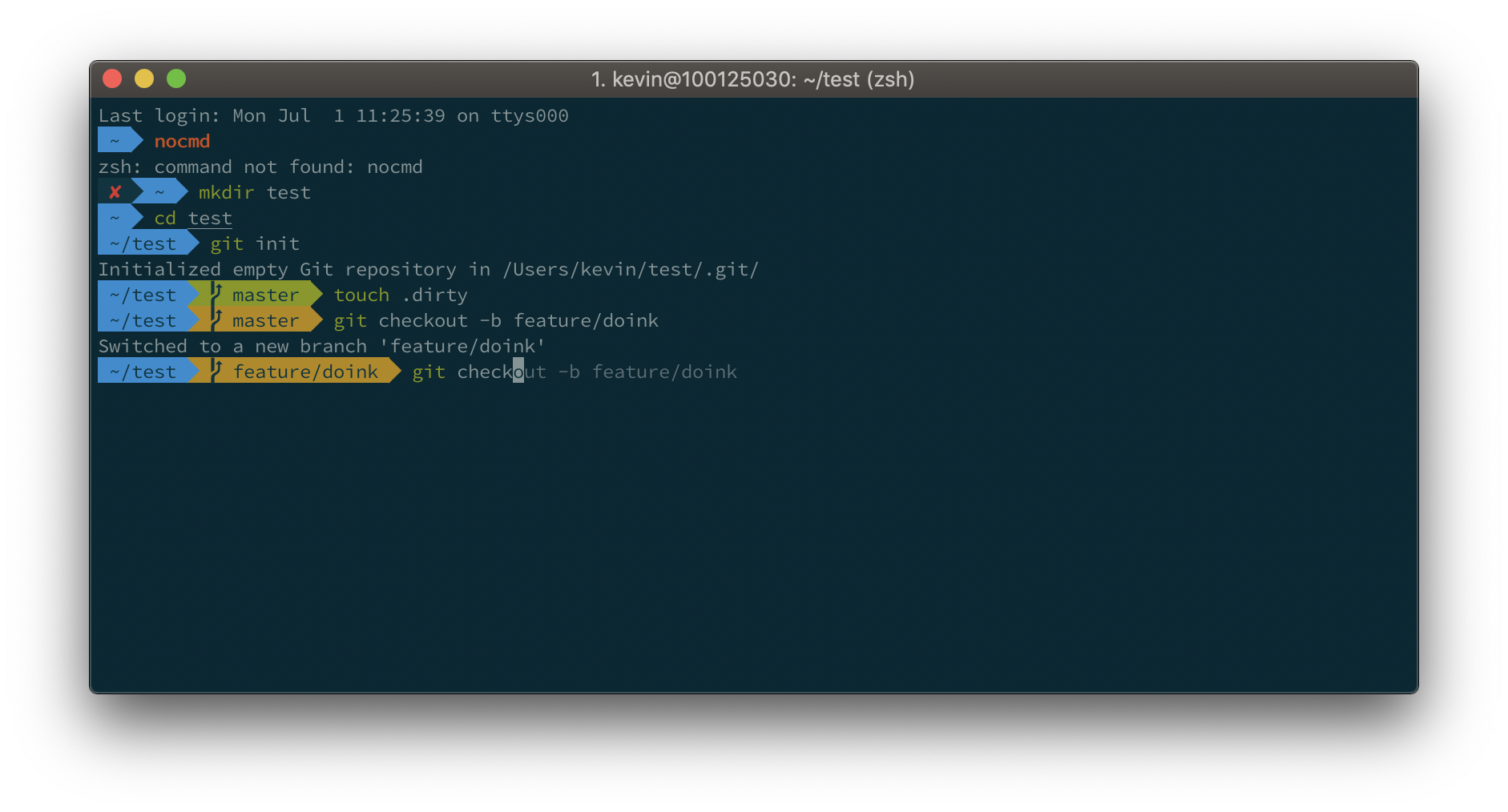
| function parse_git_dirty() { | |
| git diff --quiet --ignore-submodules HEAD 2>/dev/null; [ $? -eq 1 ] && echo "*" | |
| } | |
| # gets the current git branch | |
| function parse_git_branch() { | |
| git branch --no-color 2> /dev/null | sed -e '/^[^*]/d' -e "s/* \(.*\)/\1$(parse_git_dirty)/" |
- Recipes
- Anonymous GET access
- Anonymous GET access - match HTTP referrer
- Full access for specific IAM user/role
- GET/PUT/DELETE access to specific path within a bucket
- Restricted LIST & PUT/DELETE access to specific path within a bucket
- Full access (and S3 console) for specific IAM users
- Bucket and object delete deny
| from datetime import datetime | |
| import pytz | |
| def is_dst (): | |
| """Determine whether or not Daylight Savings Time (DST) | |
| is currently in effect""" | |
| x = datetime(datetime.now().year, 1, 1, 0, 0, 0, tzinfo=pytz.timezone('US/Eastern')) # Jan 1 of this year | |
| y = datetime.now(pytz.timezone('US/Eastern')) |
| #!/usr/bin/ruby | |
| # chkconfig: 35 99 01 | |
| # description: EC2 DNS registration | |
| # processname: ec2hostname | |
| require 'aws-sdk' | |
| require 'net/http' | |
| `touch /var/lock/subsys/ec2hostname` |
| #!/bin/bash | |
| # | |
| # consul Manage the consul agent | |
| # | |
| # chkconfig: 2345 95 95 | |
| # description: Consul is a tool for service discovery and configuration | |
| # processname: consul | |
| # config: /etc/consul.conf | |
| # pidfile: /var/run/consul.pid |
1Password 5.3 for OSX, 5.2 for iOS, and 4.1.0.538 for Windows support OTP. I've been using Authy for a while now, but the fact is, I haven't really been using 2FA for some time. As mentioned by 1Password in a recent blog post, having the OTP generator and password on the same device is very much not 2FA. It's just an expiring OTP, which can help, but let's not kid ourselves too much.
With that out of the way. One of the things that was interesting to me was moving my OTP out of Authy and into 1Password. I like the control I get with 1Password, but I didn't want to have to reset all my OTP right away, that would suck. So, I got to dissecting the Authy Chrome App to see what I could do.
Run the Authy Chrome app and make sure it's unlocked.
Now, enable Developer mode in Chrome. We'll need this to inspect the background application that stores al
| #!/bin/sh | |
| # | |
| # consul - this script manages the consul agent | |
| # | |
| # chkconfig: 345 95 05 | |
| # processname: consul | |
| ### BEGIN INIT INFO | |
| # Provides: consul | |
| # Required-Start: $local_fs $network |
| #!/bin/sh -e | |
| # | |
| # NOTE: Since Docker 1.10 (February 4, 2016), it has been possible to configure the | |
| # Docker daemon using a JSON config file. On Linux, this file is normally located at | |
| # /etc/docker/daemon.json. You should use this JSON config method if you are running | |
| # a version of Docker that is at least 1.10! | |
| # Here is an example configuration that sets the docker0 bridge IP to 192.168.254.1/24: | |
| # { | |
| # "bip": "192.168.254.1/24" | |
| # } |
| -- Table information like sortkeys, unsorted percentage | |
| -- see http://docs.aws.amazon.com/redshift/latest/dg/r_SVV_TABLE_INFO.html | |
| SELECT * FROM svv_table_info; | |
| -- Table sizes in GB | |
| SELECT t.name, COUNT(tbl) / 1000.0 AS gb | |
| FROM ( | |
| SELECT DISTINCT datname, id, name | |
| FROM stv_tbl_perm | |
| JOIN pg_database ON pg_database.oid = db_id |