Last active
June 13, 2023 17:57
-
-
Save adamierymenko/7bcc66b5f7627699236cda8ac13f923b to your computer and use it in GitHub Desktop.
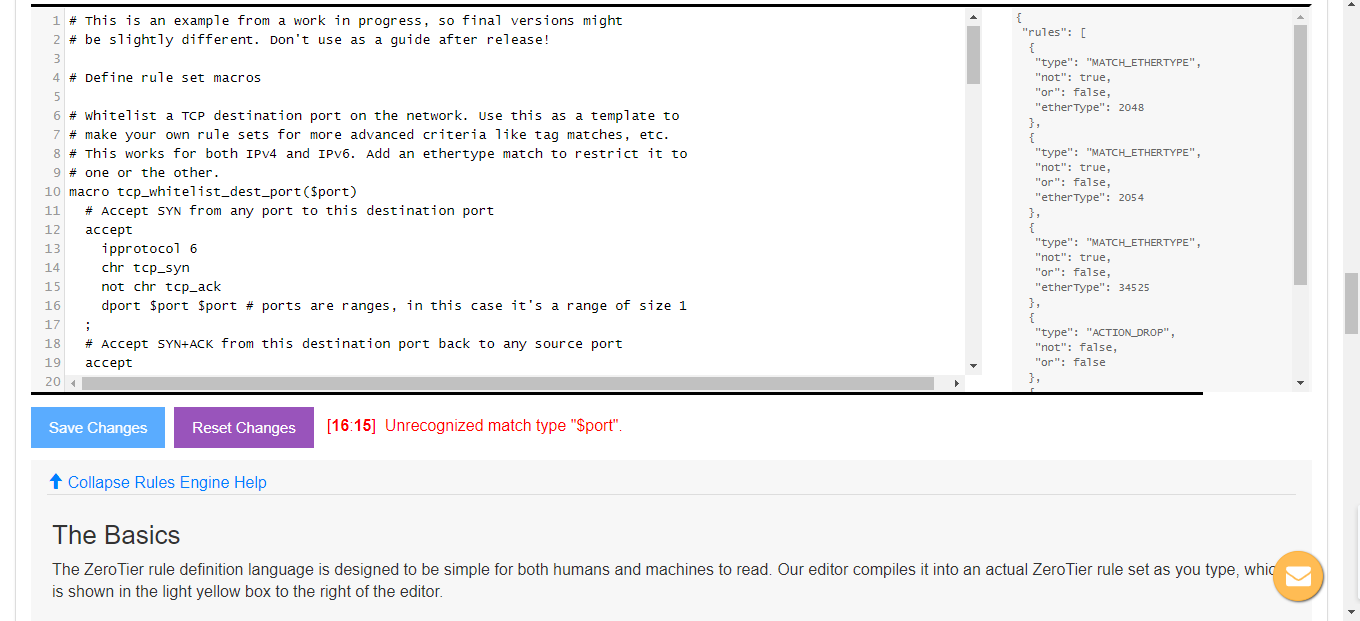
An example of what an advanced ZeroTier network rule set might look like
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| # This is an example from a work in progress, so final versions might | |
| # be slightly different. Don't use as a guide after release! | |
| # Define rule set macros | |
| # Whitelist a TCP destination port on the network. Use this as a template to | |
| # make your own rule sets for more advanced criteria like tag matches, etc. | |
| # This works for both IPv4 and IPv6. Add an ethertype match to restrict it to | |
| # one or the other. | |
| macro tcp_whitelist_dest_port($port) | |
| # Accept SYN from any port to this destination port | |
| accept | |
| ipprotocol 6 | |
| chr tcp_syn | |
| not chr tcp_ack | |
| dport $port $port # ports are ranges, in this case it's a range of size 1 | |
| ; | |
| # Accept SYN+ACK from this destination port back to any source port | |
| accept | |
| ipprotocol 6 | |
| chr tcp_syn | |
| chr tcp_ack | |
| sport $port $port | |
| ; | |
| ; | |
| # To whitelist TCP we end by permitting all non-SYN TCP packets. SYNs that | |
| # don't match will fall through and either be dropped at the end or will | |
| # get picked up by a capability. | |
| macro tcp_whitelist_end | |
| accept | |
| ipprotocol 6 | |
| not chr tcp_syn | |
| ; | |
| ; | |
| # Create a "superuser" capability that we can assign to a few members that | |
| # should be allowed to do anything. This could be useful for e.g. an active | |
| # vulnerability scanner. | |
| cap superuser | |
| id 10000 # capabilities must have unique IDs, range 0 to UINT32_MAX | |
| accept; # accept with no match criteria = always accept | |
| ; | |
| # A tag we might use to group devices together as e.g. members of the same | |
| # company department. | |
| tag department | |
| id 1000 # Tags have arbitrary 32-bit IDs like capabilities | |
| enum 100 accounting | |
| enum 200 sales | |
| enum 300 finance | |
| enum 400 legal | |
| enum 500 engineering | |
| ; | |
| # Rules for this network | |
| # Allow only IPv4 (and ARP) and IPv6. Drop other traffic. | |
| drop | |
| not ethertype 0x0800 # ... and ... | |
| not ethertype 0x0806 # ... and ... | |
| not ethertype 0x86dd # (multiple matches in an action are ANDed together!) | |
| ; | |
| # Watch all TCP connections in real time. We use two security monitoring | |
| # destinations. One will get all TCP SYN, RST, or FIN packets from the | |
| # inbound side of each sender-receiver pair. Another will get them from | |
| # the outbound side. This lets us detect hosts that are not complying | |
| # with rules by looking for differences in reported TCP traffic as well | |
| # as preventing dupes at each observer. | |
| tee 128 deadbeef00 | |
| ipprotocol 6 | |
| chr inbound # receiver side | |
| chr tcp_syn,tcp_rst,tcp_fin # multiple characteristics in the same match rule are ORed (any bit set will match) | |
| ; | |
| tee 128 deadbeef01 | |
| ipprotocol 6 | |
| not chr inbound # sender side | |
| chr tcp_syn,tcp_rst,tcp_fin # multiple characteristics in the same match rule are ORed (any bit set will match) | |
| ; | |
| # Allow only HTTP and HTTPS TCP traffic on this network | |
| include tcp_whitelist_dest_port(80) | |
| include tcp_whitelist_dest_port(443) | |
| # A variant on a normal TCP whitelist to allow ssh only between | |
| # members tagged as part of the same department. Could also make | |
| # this a macro but we only need it once here. | |
| accept | |
| tdiff department 0 # no difference | |
| ipprotocol 6 | |
| chr tcp_syn | |
| not chr tcp_ack | |
| dport 22 22 # ports are ranges, in this case it's a range of size 1 | |
| ; | |
| # Accept SYN+ACK from this destination port back to any source port | |
| accept | |
| tdiff department 0 # no difference | |
| ipprotocol 6 | |
| chr tcp_syn | |
| chr tcp_ack | |
| sport 22 22 | |
| ; | |
| # End of TCP whitelists | |
| include tcp_whitelist_end | |
| # Allow all UDP, ICMP, and IGMP | |
| accept ipprotocol 17; | |
| accept ipprotocol 1; | |
| accept ipprotocol 2; |
Hi @adamierymenko. I want to have a node that can start connection and connect to all other nodes but I dont want other nodes to see anyone. It's possible?
I have made it like this:
# Drop not wanted stuff
drop
not ethertype ipv4 # frame is not ipv4
and not ethertype arp # AND is not ARP
and not ethertype ipv6 # AND is not ipv6
or not chr ipauth # OR IP addresses are not authenticated
;
# Drop TCP SYN,!ACK packets (new connections) not explicitly whitelisted above
break # break can be overridden by a capability
chr tcp_syn # TCP SYN (TCP flags will never match non-TCP packets)
and not chr tcp_ack # AND not TCP ACK
;
# Create a capability called "superuser" that lets its holders override all but the initial "drop"
cap superuser
id 1000 # arbitrary, but must be unique
accept; # allow with no match conditions means allow anything and everything
;
# Accept other packets
accept;
can anyone help me? I just wan't to redirect all traffic to my vpn server via traffic forwading
Public ip dependency can anyone help when i am working from home my public ip is different and the server is not accessible.
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Unrecognized match type "$port".