- https://www.documentcloud.org/documents/2722196-Motion-to-Vacate-Brief-and-Supporting-Declarations.html#document/p22/a279957
- http://www.zdziarski.com/blog/?p=5743
- http://www.zdziarski.com/blog/?p=5645
- http://daringfireball.net/
- https://www.schneier.com/blog/archives/2016/02/decrypting_an_i.html
- http://www.wired.com/2016/02/apple-fbi-privacy-security/
E. The Resources And Effort Required To Develop The Software Demanded By The Government The compromised operating system that the government demands would require significant resources and effort to develop. Although it is difficult to estimate, because it has never been done before, the design, creation, validation, and deployment of the software likely would necessitate six to ten Apple engineers and employees dedicating a very substantial portion of their time for a minimum of two weeks, and likely as many as four weeks. Neuenschwander Decl. ¶ 22. Members of the team would include engineers from Apple’s core operating system group, a quality assurance engineer, a project manager, and either a document writer or a tool writer. Id.
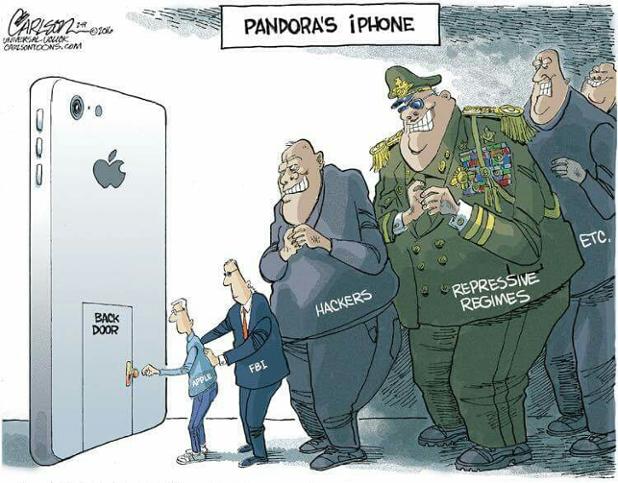
As others point out, Apple can do what the FBI is requesting, but the cost/burden is unreasonable. FBI wants a tool to recover data that fundamentally does not exist. This new design needs to be tested on multiple devices to ensure it won't break or destroy any data. Others have explained how this process works might play out, it is equivalent to creating a new product.
Every product needs to be signed by Apple using it's code signing key. This signature produced by this key is a social contract in which Apple affirms that this product is an official representation of Apple. Once signed, any other piece of software signed with the same key can trust that it is from Apple. The signing key is what ties human policy to technology.
If Apple creates the product the FBI wants, it invalidates Apple's own signing key because the product does not reflect Apple's design or policies, or product requirements. Apple considers it to be malware. If code or a product that does not meet Apple's requirements is signed by Apple's signing key, then their signing key immediately becomes corrupt, invalid, compromised, and basicaly can't be used by Apple again to make any secure products.
These are steps Apple might take to recover the value of their signing key, if it becomes compromised, or is going to become compromised:
- Obtain a new signing key
- Create new version of iOS
- Introduce new signing key as alternative acceptable key
- Force upgrade all iOS devices in the world with new alternate signing key. Make sure not to update "that iPhone" but all the others, definitely everyone that is innocent and doesn't want to be vulnerable to a compromised key.
- Create new version of iOS
- Blacklist old signing key
- Use new alternate key to sign new iOS
- Force upgrade all iOS devices in the world with new version of signing key and old one blacklisted. Make sure not to update "that iPhone" but all the others, definitely everyone that is innocent and doesn't want to be vulnerable to a compromised key.
- Create malware iOS using the old key
- Sign FBIos using old key
- update phone, do the hack
Following this series of steps would prevent the rest of the world, and Americans from the vulnerabilities introduced by the FBI's requests. The order of steps matters in order to prevent any mistakes from re-occurring. It's important to consider that FBI is asking for remote access, and that Apple has explained that new technology and documentation and protocols would need to be created and FBI would need to be trained on these tools. Given that they had trouble following Apple's directions in retaining the forensic validity of the device, one has to question if they would be able to appropriately care or handle the creation of a highly valuable and vulnerable target.