Over the past one year, I have been working on PHP and a few other languages and it took me quite some time to actually learn about various types of attacks on web servers and how to avoid them. From then on, I have been helping out others around me and finally decided to write an article on it as well.
So what is code injection or an injection attack? Quoting from Wikipedia:
Code injection is the exploitation of a computer bug that is caused by processing invalid data, which can be used by an attacker to inject code into a computer program to change the course of execution”.
Basically it refers to an unsanitized user input vulnerability, which can be used by a malicious user to run your code in a way it's not intended to. The next question is, why is it necessary to know about them? And the answer is obviously so that your web server/application does not have such vulnerabilities!
This article would give a basic introduction to such attacks, primarily for php applications using an SQL database. So before proceeding i expect you to know
html/css
php
javascript
Let us start with something simple. Consider these two files on your server:
index.html
<html>
<body>
<form action='submit.php' method='get'>
Enter your name : <input type='text' name='name' /><br />
<input type='submit' value='Submit' />
</form>
</body>
</html>
and
submit.php:
<?php
echo "welcome ".$_GET['name'];
?>
So you get the user's name in index.php and print it in submit.php. Quite simple and straightforward isn't it? But such a code could make you vulnerable to a dozen attacks!
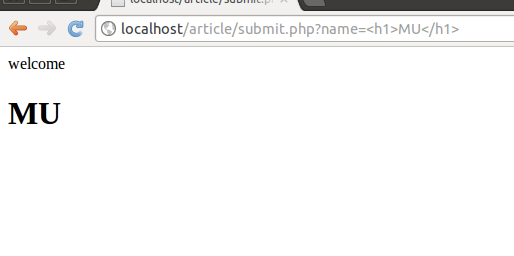
For example let us say a person (call him MU (malicious user)) wants to try something different and hence inputs:
“<h1>MU</h1>”
Then the output would be:
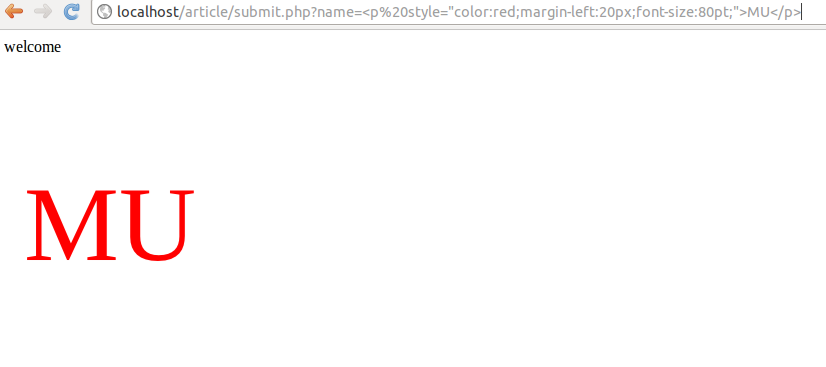
let us say MU decides to play a little more and tries to insert some style as well
so he inputs:
“<p style=%22color:red;margin-left:20px;font-size:80pt;>MU</p>”
And the output he gets is:
You can check out the url for the input MU gave (since it was a get request).