The figure below calls out
- The netfilter hooks
- The order of table traversal
netfilter hooks
+-----------> local +-----------+
| process |
| |
| |
| |
| v
MANGLE +-------------+--------+
FILTER | | +----------------------+ RAW
SECURITY | input | | | conntrack
SNAT | | | output | MANGLE
+------+---------------+ | | DNAT
^ +-------+--------------+ routing
| | FILTER
| | SECURITY
| +---------------------+ | +-------------+
+-----------+ | | +-------> | |
+--> |pre routing+---- route -----> | forward | |post routing +---->
| | lookup | +------------> | |
+-----------+ +---------------------+ +-------------+
RAW MANGLE MANGLE
conntrack FILTER SNAT
MANGLE SECURITY
DNAT
routing
- Incoming packets destined for the local system: PREROUTING -> INPUT
- Incoming packets destined to another host: PREROUTING -> FORWARD -> POSTROUTING
- Locally generated packets: OUTPUT -> POSTROUTING
- The iptables firewall uses tables to organize its rules
- These tables classify rules according to the type of decisions they are used to make
- Within each iptables table, rules are further organized within separate "chains"
- Chains map to netfilter hooks
- filter: Do not modify traffic. Mostly used for firewalling
- nat:
- mangle: used to modify or mark packets: Mark is on the skbuf and not on the packet itself
- raw: used to help skip conntrack
- security used by selinux
- raw : Used to bypass connection tracking
- (connection tracking enabled)
- mangle
- nat (DNAT)
- (routing decision)
- filter
- security
- nat (SNAT)
- Rules are placed within a specific chain of a specific table
- Note: The table determines order of evaluation
- A target is the action that are triggered when a packet meets the matching criteria of a rule.
- Terminating targets: Terminating targets perform an action which terminates evaluation within the chain and returns control to the netfilter hook
- Non-terminating targets: Non-terminating targets perform an action and continue evaluation within the chain
- special class of non-terminating target: the jump target
- user-defined chains can only be reached by "jumping" to them from a rule via the jump target
- and they can jump to other chains
iptables -N <chain name> iptables -A INPUT -p tcp -j <chain name> - if a packet is ACCEPTed within one of the sub chains, it will be ACCEPT'ed in the superset chain also and it will not traverse any of the superset chains any further (in that table!). However, do note that the packet will traverse all other chains in the other tables in a normal fashion.
- -j RETURN: will cause the current packet to stop traveling through the chain (or sub-chain)
- -j ACCEPT : the rule is accepted and will not continue traversing the current chain or any other ones in the same table. Note however, that a packet that was accepted in one chain might still travel through chains within other tables, and could still be dropped there
- -j DNAT : only available within PREROUTING and OUTPUT chains in the nat table, and any of the chains called upon from any of those listed chains
- -j SNAT: valid only in nat table, within the POSTROUTING chain
- -j DROP: Drops the packet, right there right then
- -j REJECT: Sends a response back (unlike drop). Valid in the INPUT, FORWARD and OUTPUT chains or their sub chains
- -j LOG: Note: Does not work on namespaces. Also can fill up your kernel log.
iptables -A INPUT -p tcp -j LOG --log-prefix "INPUT packets" - -j ULOG: packet information is multicasted together with the whole packet through a netlink socket. One or more user-space processes may then subscribe to various multicast groups and receive the packet
- -j MARK: Only valid in mangle table.
Note that the mark value is not set within the actual package, but is a value that is associated within the kernel with the packet. In other words does not make it out of the machine
iptables -t mangle -A PREROUTING -p tcp --dport 22 -j MARK --set-mark 2 - -j MASQUERADE: Similar to SNAT but used on a outbound network interface when the outbound IP can change. Say a DHCP interface Only valid within the POSTROUTING
- -j REDIRECT: redirect packets and streams to the machine itself. Valid within the PREROUTING and OUTPUT chains of the nat table. It is also valid within user-defined chains that are only called from those chains
- iptables can use extended packet matching modules with the -m or --match options, followed by the matching module name
- Some important ones
- connmark [!] --mark value[/mask] Matches packets in connections with the given mark value (if a mask is specified, this is logically ANDed with the mark before the comparison).
- conntrack
- ipvs
- mark
- redirect This target is only valid in the nat table, in the PREROUTING and OUTPUT chains, and user-defined chains which are only called from those chains. It redirects the packet to the machine itself by changing the destination IP to the primary address of the incoming interface (locally-generated packets are mapped to the localhost address, 127.0.0.1 for IPv4 and ::1 for IPv6).
- https://www.digitalocean.com/community/tutorials/a-deep-dive-into-iptables-and-netfilter-architecture
- https://www.netfilter.org/documentation/HOWTO/netfilter-hacking-HOWTO-3.html
- https://www.frozentux.net/iptables-tutorial/chunkyhtml/c3965.html
- http://ipset.netfilter.org/iptables-extensions.man.html
- http://ebtables.netfilter.org/br_fw_ia/br_fw_ia.html
+-----------> local +-----------+
| |
| |
| |
| |
| v
+-------------+--------+
| | +----------------------+
| input | | |
| | | output |
+------+---------------+ | |
^ +-------+--------------+
| |
| |
| +---------------------+ | +-------------+
--------------- +-----------+ | | +-------> | |
| brouting | --> |pre routing+---- route -----> | forward | |post routing +---->
| | | | lookup | +------------> | |
-------------- +-----------+ +---------------------+ +-------------+
- The broute table has the BROUTING chain.
- The filter table has the FORWARD, INPUT and OUTPUT chains.
- The nat table has the PREROUTING, OUTPUT and POSTROUTING chains.
Port forwarding between three PC's:
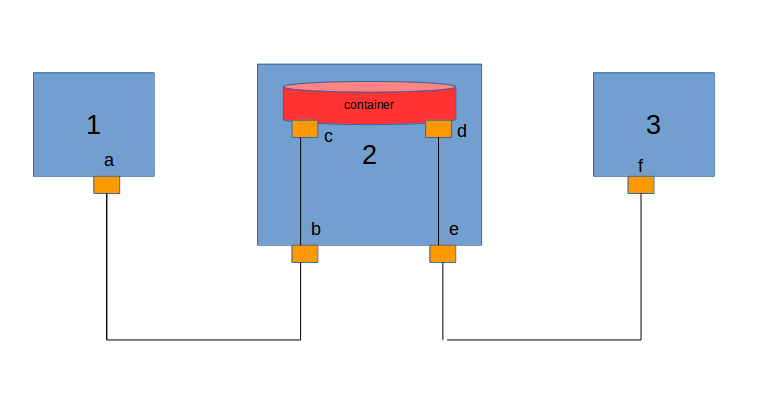
Architecture
configuration:
PC 1 eth0(a) - 172.xxx.xx.xxx
PC 2 br0(b) - 172.xxx.xx.xx
PC 2 br1(e) - 192.xxx.xx.xx
PC 2 container eth0(c) - 172.xxx.xx.xx
PC 2 container eth1(d) - 192.xxx.xx.xx
PC 3 eth0(f) - 192.xxx.xx.xx
I was able to ping from PC 1 to PC 3 through the container in PC 2. To ping I have added route tables in PC 1 and PC 3. I was able to ping in all the combinations. finally when I ping from PC 1 to PC 3 packet goes from (a)->(b)->(c)->(d)->(e)->(f)
Now I have hosted a apache server in PC 1 and stored PHP sample program in /var/www/html then I open browser in PC 3 I was able to access the PHP file from PC 1 via browser.
Now I deleted IP tables. I should access the PC 1 sample PHP in PC 3 using port forwarding via (a)->(b)->(c)->(d)->(e)->(f)? Where should I preroute? can anyone say the exact steps to port forward?